Table of Contents
Navigating the March 31 transmission deadline and new supervisory cycle
March 31 represents the hard deadline for National Competent Authorities (NCAs) to transmit Registers of Information (RoI) to the European Supervisory Authorities (ESAs). These are the troika of EU financial regulators, including the EBA (European Banking Authority), EIOPA (European Insurance and Occupational Pensions Authority) and ESMA (European Securities and Markets Authority).Although firms might be tempted to treat this inflection point as an administrative handover, it is when data enters the ESA’s centralized processing engine - for good. From there, the ESAs launch their own supervisory cycle. The regulators use your March 31 snapshot to identify systemic risks, designate new critical providers and prioritize future inspections.
To help you navigate this era of active oversight, this guide walks through the distinct phases of the 2026 supervisory cycle, explores the Digital Operational Resilience Act (DORA) pillars you must now defend and examine the digital tools required to stay ahead.
Phase 1: The data quality (DQ) audit
Since the DORA Act went into force in January 2025, financial entities have had to maintain comprehensive registers of their contracts with ICT (Information and Communications Technology) third-party service providers. This maintenance and reporting obligation applies at three levels:
- Entity level: The standalone reporting level. This applies to a single licensed financial entity that is not part of a larger group.
- Sub-consolidated level: The intermediate level. This applies when a financial entity is part of a larger group, sitting under an intermediate parent undertaking.
- Consolidated level: The highest EU level. This is the top-tier reporting for a group of financial entities in the EU. It is the single most important view the ESAs have to identify macro-concentration risk.
The registers serve three critical functions:
- For financial entities: An internal tool to monitor their own ICT third-party risk.
- For the NCAs: A source of information to supervise how financial entities manage ICT third-party risk.
- For the ESAs: A source of information for designating CTPPs.
After receiving RoI from national authorities, the ESAs perform their own assessment. This sequential, two-tier process covers:
- Technical integration: Gate-keeper tier. Validates ZIP package naming and xBRL-CSV structure. Failure equals immediate rejection.
- Preliminary validation: Verifies DPM (data point model) alignment and unique identifier formatting.
The 116-point automated audit
Every register that clears these initial gates is immediately put under a final microscope. This forensic analysis applies 116 automated data quality checks across five thematic areas:
- Relational integrity (unique identifiers): Linking data points across 15 templates.
- Identity verification (LEI validity): Cross-referencing Legal Entity Identifiers (LEIs) against the global GLEIF (Global Legal Entity Identifier Foundation) database.
- Technical standard alignment (DPM content): Adhering to the EBA’s DBM members.
- Criticality markers (mandatory fields): Identifying mandatory fields for CTPP designation.
- Standardized chronology (date validity): Confirming ISO 8601 date validity.
Chances of failure are high throughout. In 2024, the ESAs held a dry run of this very exercise. Out of 1,039 submissions received, 92 immediately failed integration checks. The remaining 947 submissions were accepted. Of those, 93.5% (886 in total) triggered at least one data quality failure.
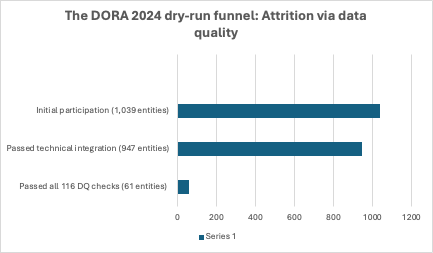
Image source: “Key findings from the 2024 ESAs Dry Run exercise”
Delving deeper, the area with the most failures was mandatory information missing. The most encountered issue was identification codes for ICT third-party service providers and their parent undertaking. The area with the second most failures was “Invalid LEI codes.” After that was “Invalid DPM value.”
Now that the Digital Operational Resilience Act applies, best effort is a thing of the past. Compliance is now binary. Submissions either pass or fail. Any entity that triggers an error is mandated to remediate and resubmit within the strict supervisory window.
Strategic recommendations for the 2026 cycle:
- Achieving absolute completeness: In the active oversight phase, an omitted contract constitutes a breach of the General Duty Clause.
- The LEI hygiene protocol: Do not wait for a rejection. Cross-reference your TPP identifiers against the GLEIF database internally. Ensure parent undertakings are correctly mapped to prevent “Identity Failure” rejections.
- Transitioning to machine-ready tools: Manual data management is a leading cause of submission failure. Firms must therefore choose a solution that runs the 116 ESA validation rules in real time. This will help ensure registers are machine-ready before even reaching NCAs.
Phase 2: Mapping the EU ecosystem via criticality assessment
The primary reason for the March 31 snapshot is to feed the criticality assessment. Once the ESAs have a clean dataset, they use it for a deep mapping of the entire EU financial ecosystem. This is a forensic look at Nth-party dependencies. Regulators trace the subterranean links connecting direct vendors, critical subcontractors and fourth-party infrastructure.
Criteria for criticality:
- Systemic impact: The ESAs measure the total value of assets and the volume of financial entities that would be paralyzed by a large-scale provider failure.
- Criticality of functions supported: Regulators prioritize providers that support critical or important functions (CIFs).
- The importance of the reliant entities: The ESAs consider whether global systemically important institutions (G-SIIs) rely on the provider.
- Degree and difficulty of substitutability: This assesses the lack of real alternatives, specifically identifying providers where firms reported no other vendor has the required capacity or technical sophistication.
- Migration complexity: This methodology flags cases where migrating away from a provider would entail prohibitive costs or significant operational risk.
Phase 3: Macro-concentration and resilience testing
Last November, the ESAs officially designated 19 CTPPs. As expected, the list was dominated by hyperscale cloud players, such as AWS, Google and Microsoft, and infrastructure giants including Equinix and Deutsche Telekom. Like an evolving map, the list will grow and contract based on the DORA 2026 snapshot.
The snapshot allows the ESAs to spot local concentration for the first time. Previously, regional dependencies, like whether too many critical payment services in a single Member State rely on the same power grid or regional data center cluster, were largely invisible to regulators.
Not anymore. In an oversight shift, the ESAs have the power to designate providers as CTTPs mid-cycle if the aggregated registers show that a regional provider has become the silent backbone for a national sector.
If a vendor you rely on is added to this list, your oversight burden shifts instantly. You must ensure your contracts provide the Lead Overseers with full access and audit rights.
TLPT: Selection by data
Another outcome of the March 31 transmission is the TLPT (Threat-Led Penetration Testing) selection notice. TLPT is a significant departure from routine security assessments. Unlike a standard scan, it is a dynamic, intelligence-based simulation. Independent “Red Team” testers mimic the exact tactics of sophisticated cyber adversaries currently targeting the financial sector.
For the 2026 cycle, NCAs will use your RoI data to apply a two-layer selection approach.
- Layer 1 (Quantitative): High-level thresholds including total asset size, market share and transaction volume.
- Layer 2 (Qualitative): A risk-based assessment focusing on supply chain dependencies and ICT maturity demonstrated in reporting.
If your RoI reveals you are a central node in a high-concentration vendor network, expect a notification from your NCA to perform a TLPT within the next 3-year cycle. This triggers a mandatory requirement. While you hire the testers, your contracts must guarantee that ICT providers will cooperate.
Pillars of defensible resilience
The March 31 transmission is a technical milestone. But your RoI must be backed by a mature operational framework to withstand the 2026 supervisory cycle. Regulators will use your data as a roadmap to audit these five core resilience pillars. Here is how to defend your position:
1. ICT risk management
The Digital Operational Resilience Act (DORA) requires financial entities to develop an internal governance and control framework for ICT risk management. Senior leadership must define, approve and oversee the implementation of all arrangements related to this framework.
In 2026, regulators will use your RoI to confirm whether your identified CIFs match internal risk assessments. To ensure they do, validate that your internal business impact analysis (BIA) aligns perfectly with criticality in your submission.
Discrepancies between your RoI and your internal risk register are immediate red flags for NCAs.
2. Incident reporting
The DORA Act is notable for its strict incident reporting requirements. Financial entities must not only record all ICT-related incidents and significant cyber threats but also categorize these events by priority, severity and criticality of services impacted.
In 2026, ESAs are cross-referencing incident data across the Union. What does that mean? If you failed to report an incident in 2025 that your peers (or vendors) reported as “Major,” you will be flagged for under-reporting.
Your best defense is to maintain a clear audit trail of your classification logic. Be ready to defend deeming an outage “Minor” despite hitting the 2-hour downtime or 10% client impact markers.
3. Digital operational resilience testing
Although TLPT is reserved for significant firms, all entities must perform basic testing. The purpose of a digital operational resilience testing program is to assess your preparedness for handling ICT incidents, identifying weaknesses and implementing corrective measures.
In the current cycle, use your testing results to justify your ICT maturity score. If your RoI shows high vendor concentration, your resilience testing results must prove that you have specifically tested potential third-party failure points.
4. The longtail of ICT risk
Entities must ensure contracts meet DORA’s requirements. These include due diligence, information security standards and automatic termination clauses. However, the 2026 focus has shifted to fourth-party risk. And that risk stems from the subcontractors your vendors rely on.
Staying ahead of fourth-party risk entails establishing a line of sight. Your defense during a supervisory audit will rely on your ability to show that you did not just stop at your direct vendor but also identified the critical subcontractors that could cause a domino effect.
Ensure that the exit strategies you include in your contracts are not just templates. Regulators are keen to see that you have a viable plan to migrate services if a concentrated provider fails.
5. Information sharing
DORA's purpose is to enhance the level of digital operational resilience across the Union. Regulators encourage participation in cyber-threat and vulnerability intelligence-sharing arrangements.
Highlight your participation in Information Sharing and Analysis Centers (ISACs). During the supervisory cycle, this demonstrates that you are proactively managing threats rather than merely reacting to them.
Overcoming the technical hurdle
The ESAs supported the 2024 dry run with a suite of helper tools: templates for Excel, draft data point models and a basic Excel-to-CSV converter. That support is over. Nor are regulators accepting simple CSV uploads or Excel workbooks. Submissions must now be delivered as a validated ZIP package containing:
- Naming convention: The name of the ZIP file must adhere to the naming convention.
- xBRL-CSV files: Data must be formatted to the precise EBA DPM 4.0 taxonomy.
- JSON metadata: A header file describing the nature of the report and the entity.
Relational integrity matters just as much as file type. In a validated ZIP package, even a single mismatched ID will trigger automatic rejection.
Digital tools: The single source of truth
While technical requirements harden, best effort no longer suffices. This means manual reporting introduces significant operational risk.
Forward-thinking financial entities have moved away from disconnected spreadsheets and toward integrated resilience workspaces. While a spreadsheet is a static document, business continuity software provides a live, centrally governed environment where your resilience data resides.
By centralizing the Digital Operational Resilience Act (DORA) data, you maintain a state of defensible resilience, eliminating the scramble to report.
How business continuity software helps:
- Integrated BIA and criticality mapping: Built-in BIA tools guide you step-by-step to identify your CIFs. This helps to ensure that the criticality markers you report on are backed by data-driven insights.
- Dynamic dependency mapping: The ESAs are prioritizing audits on macro-concentration. Digital software allows you to visualize and track dependencies between business activities, supporting assets and ICT third-party providers. When a vendor is flagged as at risk, you can see exactly which of your critical functions are impacted instantly.
- Data foundation: In the dry run, most firms failed because of data fragmentation. By using a single platform for third-party risk management and operational resilience, you can easily keep unique identifiers (like LEIs) and vendor roles consistent across the entire organization. When it is time to fill out the mandatory templates, your data is already reconciled and clean.
- Proactive resilience monitoring: Through flexible dashboards and analytics, you can monitor resilience testing results in real time. This digitized audit trail allows you to justify your ICT maturity score.
Conclusion: The beginning of active oversight
Far from the finish line, the March 31 transmission is the beginning of a permanent supervisory regime. The data you submit will dictate your TLPT selection, CTPP designations and supervisory priority for years to come.
In this new era, compliance can no longer be static. By leveraging digital tools to manage the complexity of DORA, firms can move past the technical reporting hurdles. They can instead prioritize what the regulation intended: building a truly resilient organization that can withstand any disruption.
Ready to move beyond manual compliance?
Don’t let the 2026 supervisory cycle catch you off guard. See how Noggin’s automated business continuity software provides the single source of truth you need for a defensible DORA strategy. Request a demo, today!